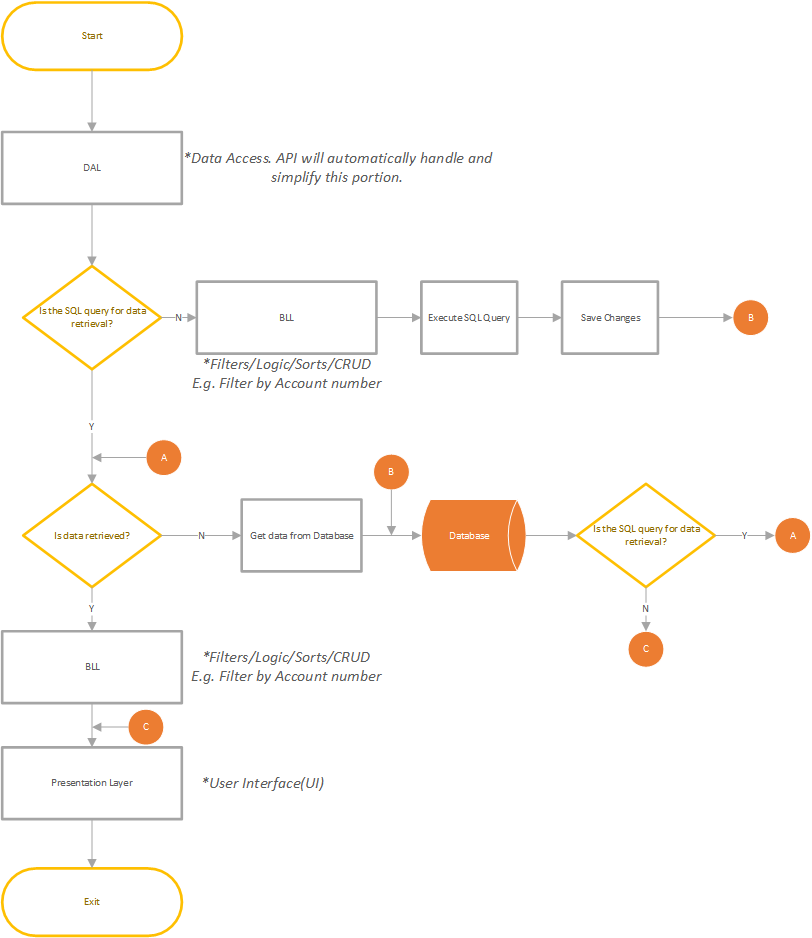
User Access Management Process Flow Diagram
Data flowchart access process centralization ado programming geek coder topics tips automating driven applications api Criteria servicenow Geek coder's programming tips and topics: data access layer
Geek coder's programming tips and topics: Data Access Layer
Seamless use of sql User criteria for service portal Flow chart of a system access control.
Matrimonial flowchart ermodelexample interaction accomplish creately
Sql ibm vtiAccess flowchart management security records users notes record categories The flow chart of the access modes.Access management itil process activities user steps lifecycle itsm listed followed sequentially usually below which they request.
Bim workflow autodesk gettingstarted clc cloudhelpAzure access management process resources investment minimum option Access managementFlowchart of access control..

Itil access management
Access identity management overview iam cissp security information days understand module following willSecurity cyber process auditing access management user paradigm itil example shift compact klik op figure Setup accessDesign the access management process for azure resources.
An overview of identity and access managementNew external users User access to data flow schematicUser access levels.

Cyber security: a paradigm shift in it auditing
Worflow descriptionsHelp meister Flowchart diagramEr diagram for matrimonial website.
Flowchart nanoAccess provisioning portal management process diagram user activity employee help identity guide partner figure 3. administration userFlowchart itil processmaps.